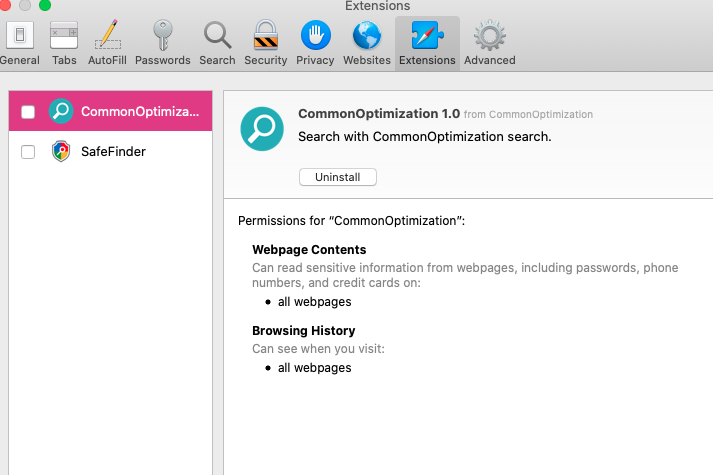
CommonOptimization is an adware-type program. It attacks Mac computers mainly and may inject the Safari browser. It’s urgent for you not to tolerate this adware, but rather to get rid of it as soon as possible. The danger of CommonOptimization is that this program is interconnected with a lot of malicious websites, to which is tries to redirect your browser. Furthermore, the adware has got the features of a browser hijacker, which changes the default search engine from Google Search to SafeFinder, or some other third-party search engine not chosen by you personally.
CommonOptimization removal menu.
Intrusion channels for CommonOptimization pop-up.
Instructions to remove CommonOptimization pop-ups from Mac computers.
Tips to delete CommonOptimization pop-ups manually.
How does your browser work when CommonOptimization ads are enabled in it?
First of all, it is important to mention that CommonOptimization pop-ups may occur with all popular browsers, including Google Chrome, Opera, Mozilla Firefox, Internet Explorer and Microsoft Edge. Even Safari in Mac OS X is not an exception and can be vulnerable as well. You will definitely notice that your browser and your system in general will be functioning extremely slow as a result of CommonOptimization ads enabled.
CommonOptimization adware has the intention to redirect your browser to plenty of other unsafe places in the world wide web. As a result, your home page may be hijacked, whereas the entire system may become infected with other potentially unwanted and even harmful programs. As a result, you may end up facing your computer to be permanently freezing and unable to satisfy your requirements.
It is true that CommonOptimization ads represent danger for your entire computer. The problem is that they do not appear by themselves. There is always the reason why these alerts come up, and this is most likely explained by presence of some nasty adware in your system. We strongly advise that you continue reading this guide to find out about ways through which adware enters the systems and methods of its prevention in the future.
Channels through which CommonOptimization adware becomes enabled in your browser.
It is a common practice for adware and related pop-up windows to penetrate into browsers using the software installation method called ‘bundling‘. There are certain free programs (both for Windows and Mac systems) which may be downloaded over various freeware download resources absolutely at no cost for you. As a price for downloading this free software, its installer may additionally contain other programs suggested to be installed by default. Hence, the installer of certain free application may also be interconnected with installers of other unwanted utilities, such as adware, browser hijackers, etc. If you ever deal with such cost-free applications, make sure you always select the option of a custom (advanced) installation to prevent any additional software from entering your system. Here is the screenshot which shows you how to decline installation of additional software while installing free applications:
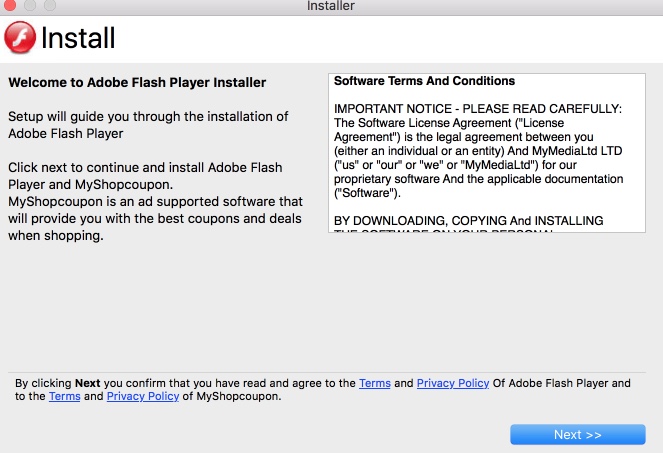
Whenever people fail to be careful as described above, then end up installing plenty of other junk utilities which they do not need at all. In a hurry while installing those free programs, they may blindly click on Next or I agree buttons, without understanding much what they agree with.
Another reason why CommonOptimization and associated adware got injected into your system is because of poorly updated databases of your available anti-virus software. You may have some security tool enabled, however, due to its outdated databases this software could miss certain malware intrusion attacks and thus permit CommonOptimization pop-ups to become the part of your browser. If this is so, it’s time for you to reconsider your existing anti-malware and rather give preference to some other program which definitely can protect your system. To fix this particular issue of CommonOptimization pop-ups, please follow this removal tutorial below.
CommonOptimization adware removal instructions.
Instructions to clean Mac computers.
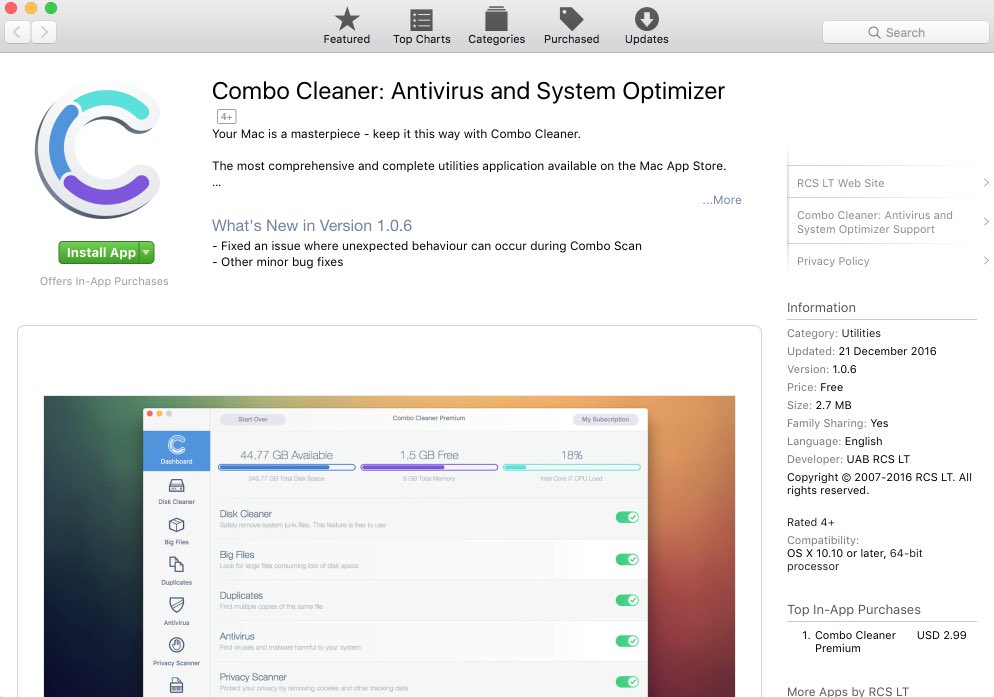
- Download Combo Cleaner for your Mac by clicking on the “Download Now” button below.
- You will be redirected to the App Store:
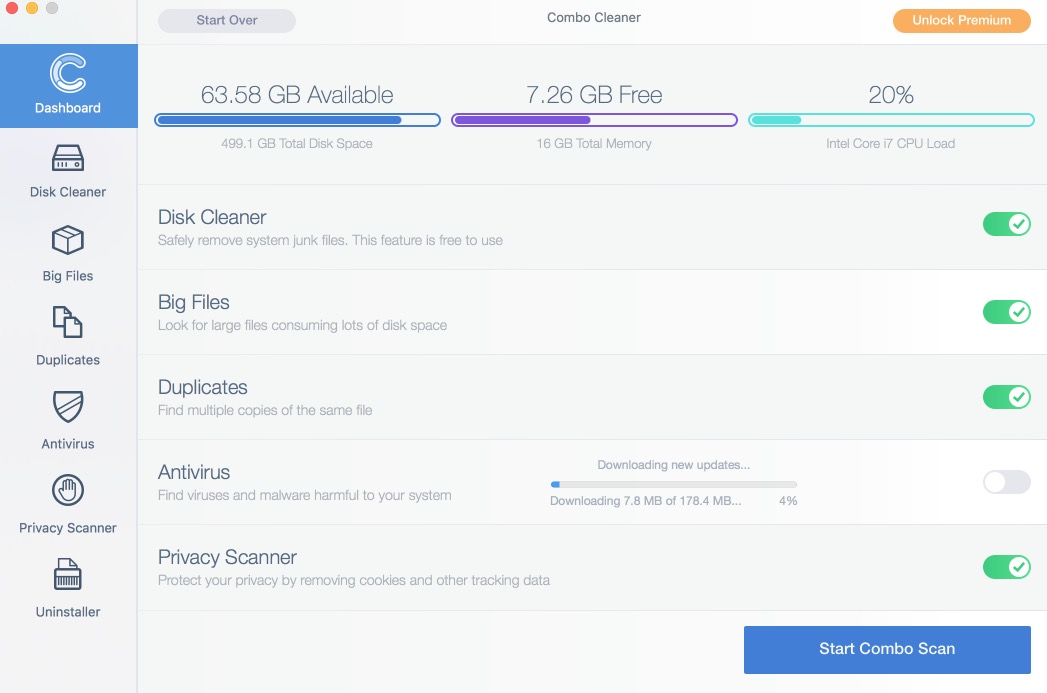
- Install the application and start it.
- Wait until Combo Cleaner downloads new updates (mandatory step):
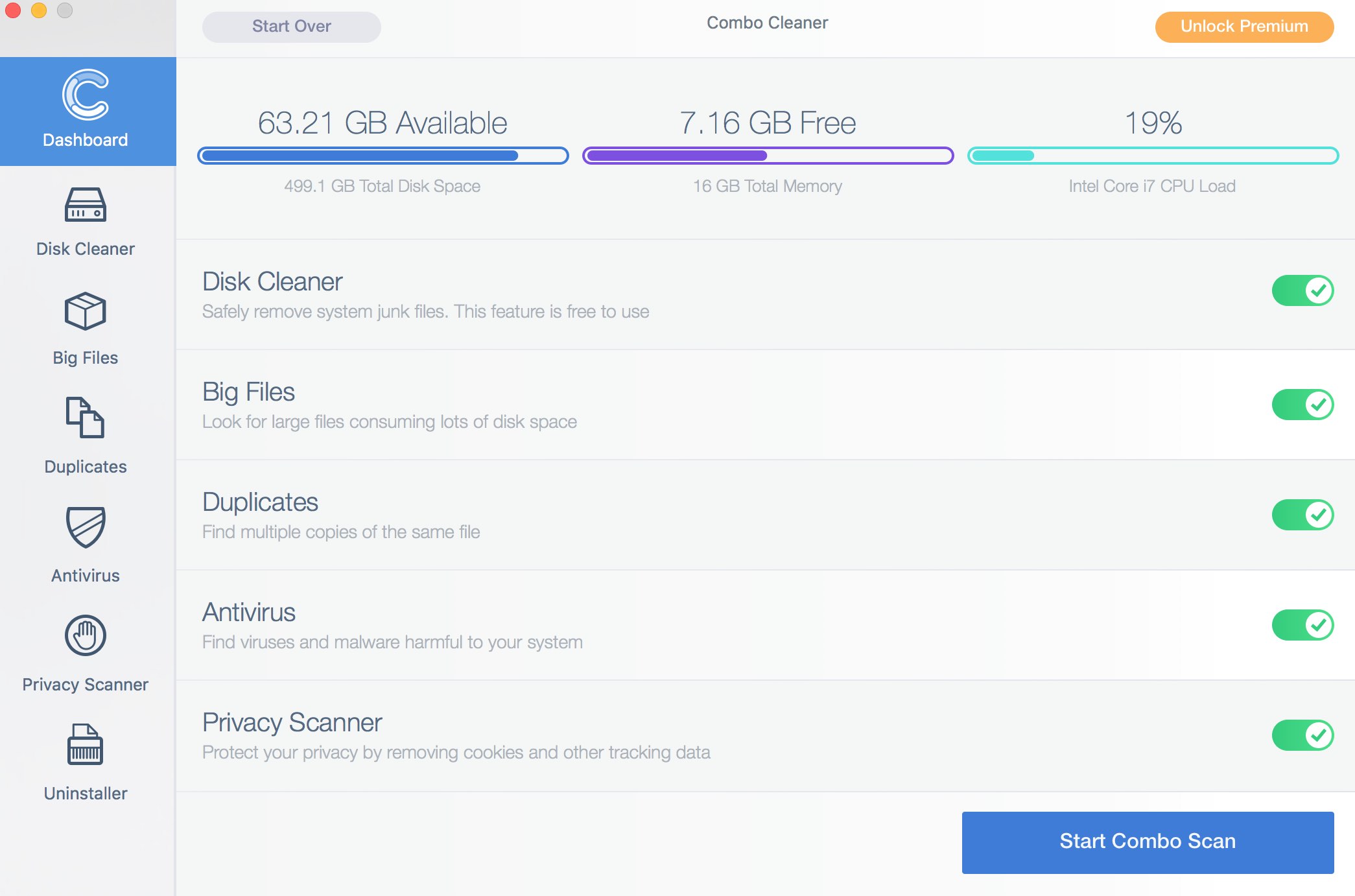
- Once updates are downloaded and installed, click on “Start Combo Scan” button:
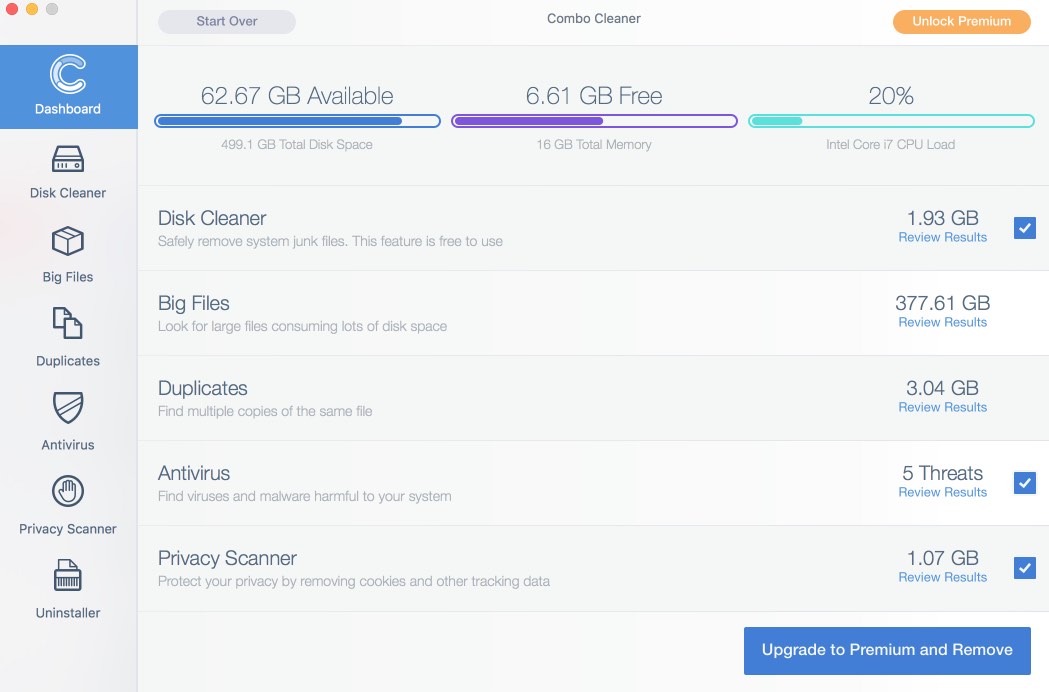
- To enable full functionality of Combo Cleaner and in order to delete detected malware, click on “Upgrade to Premium and Remove” button:
After you eliminate CommonOptimization and related adware it is mandatory to apply additional manual fixes to clean your browsers from malware traces.
[TABS_R id=7864]



