Esurf.biz has the “fame” of a new nasty hijacker infecting many widely used browsers today. The hijacker may attack Google Chrome, Opera, Mozilla Firefox, Internet Explorer, and even Microsoft Edge browsers. All such unexpected events take place after you fail to be duly attentive and install different free applications.
Esurf.biz changes the Desktop icons (shortcuts) of all these above-mentioned browsers. Actually, to remove Esurf.biz you will need to remove the remnants after chrome.exe”, firefox.exe”, opera.exe” and iexplore.exe” in the shortcut properties. In this guide we will furnish you with a free video guide explaining how to do it, and also with the automatic instructions to remove this hijacker using the powerful antispyware tool.
Esurf.biz removal menu:
- Recommended software to remove Esurf.biz automatically.
- Resetting browser settings after automatic removal of Esurf.biz.
- Video explaining how to reset your browsers affected by Esurf.biz.
- Tutorial to remove Esurf.biz manually.
- How to prevent your PC from being reinfected.
Esurf.biz hijacker also does a lot of other totally unwanted things. For example, it very soon redirects you to a lot of other illegal and quite dangerous domains. As soon as you actually start your browser in an attempt to find something important to you, Esurf.biz will come up and will bring you to all those malicious resources.
Eventually, these sites may force you to download and install a lot of other absolutely malicious applications into your computer, such as adware, browser hijackers and other totally useless software examples.
Note that the troubles related to Esurf.biz may occur after you decide to download and install some other free applications into your system. Whether you are quite active in doing so, of prefer to occasionally install some free software, – it all doesn’t matter. In all cases you must be very careful not to permit any junk software to enter your PC. Always choose the option of a custom (advanced) installation to prevent any unwanted applications from becoming the part of your system by default.
Problems with Esurf.biz and other malicious programs start happening as soon as users actually fail to be duly attentive. Typically they just click on “Next” or “I agree” buttons during freeware installation, thus permitting these malicious software to be made the part of their computers.
As we’ve said, you may get rid of Esurf.biz manually as explained in the video guide in the very end of this guide. Alternatively, you may scan your system with Plumbytes Anti-Malware and remove all possible threats from your system automatically. We believe that this is the best solution so far. Please follow the uninstall tips set forth below.
Software to get rid of Esurf.biz automatically.
Important milestones to delete Esurf.biz automatically are as follows:
- Downloading and installing the program.
- Scanning of your PC with it.
- Removal of all infections detected by it (with full registered version).
- Resetting your browser with Plumbytes Anti-Malware.
- Restarting your computer.
Detailed instructions to remove Esurf.biz automatically.
- Download Plumbytes Anti-Malware through the download button above.
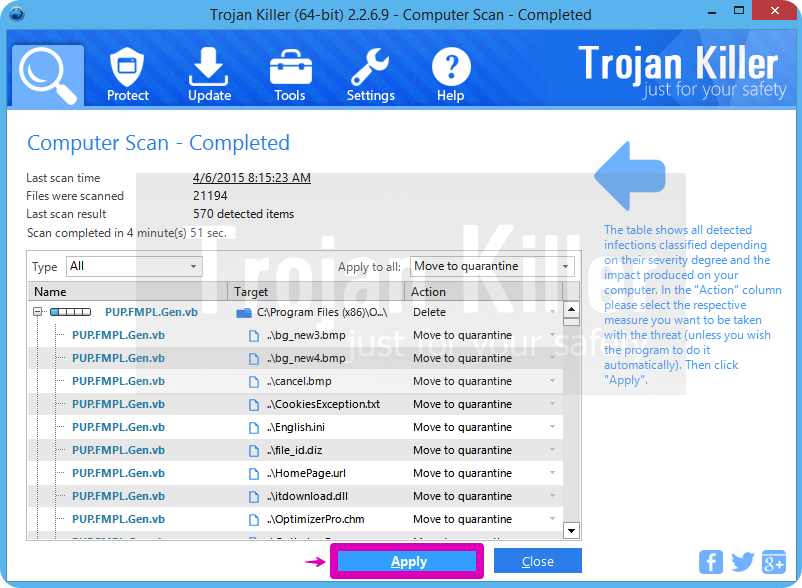
- Install the program and scan your computer with it.
- At the end of scan click “Apply” to remove all infections associated with Esurf.biz:
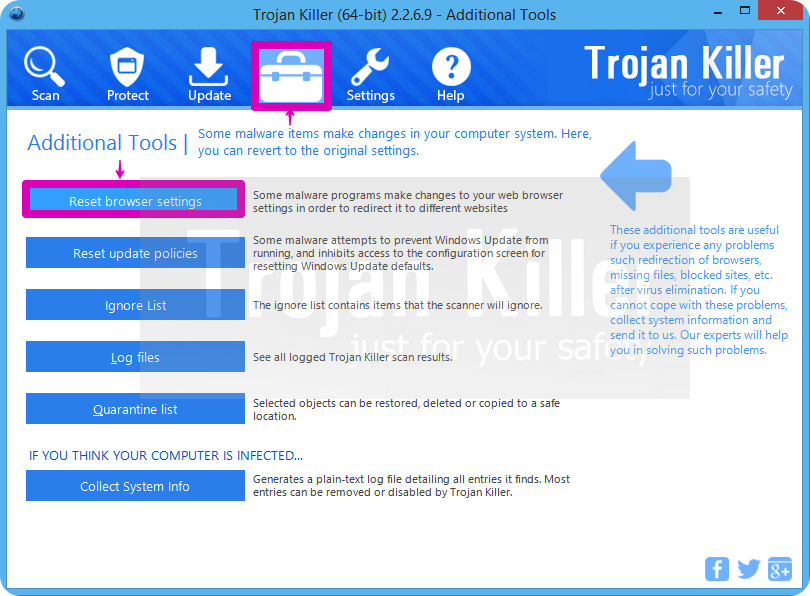
- Important! It is also necessary that you reset your browsers with Plumbytes Anti-Malware after removal of Esurf.biz. Shut down all your available browsers now.
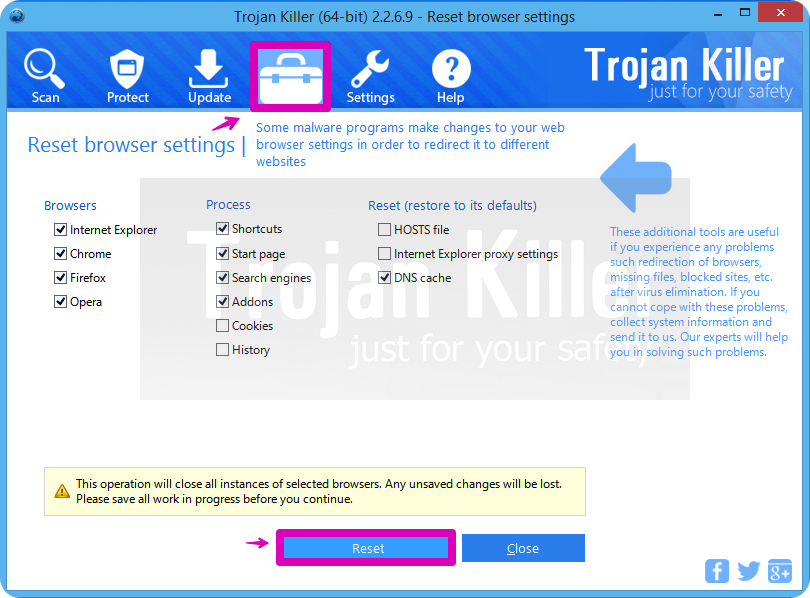
- In Plumbytes Anti-Malware click on “Tools” tab and select “Reset browser settings“:
- Select which particular browsers you want to be reset and choose the reset options.
- Click on “Reset” button.
- You will receive the confirmation windows about browser settings reset successfully.
- Reboot your PC now.
Video guide explaining how to reset browsers altogether automatically with Plumbytes Anti-Malware:
Detailed removal instructions to uninstall Esurf.biz manually
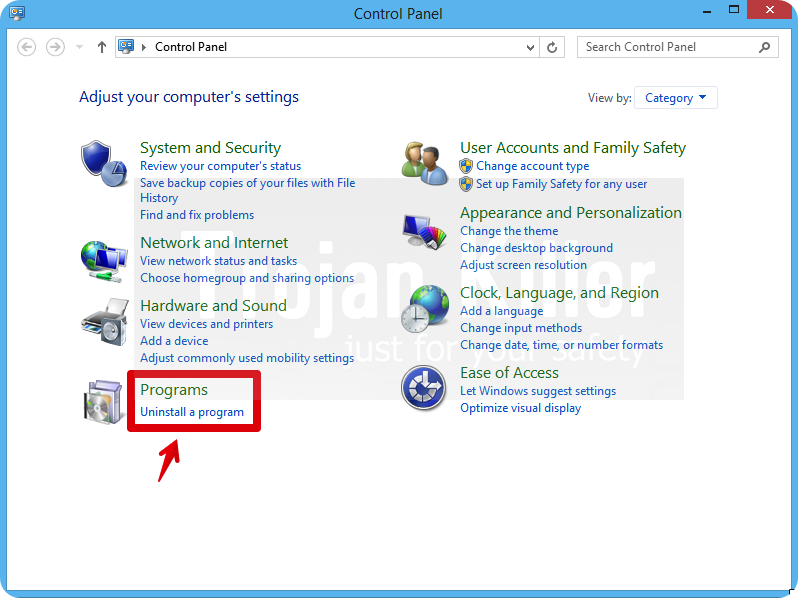
Step 1. Uninstalling suspicious applications from the Control Panel of your computer.
- Make sure that all your browsers infected with Esurf.biz are shut down (closed).
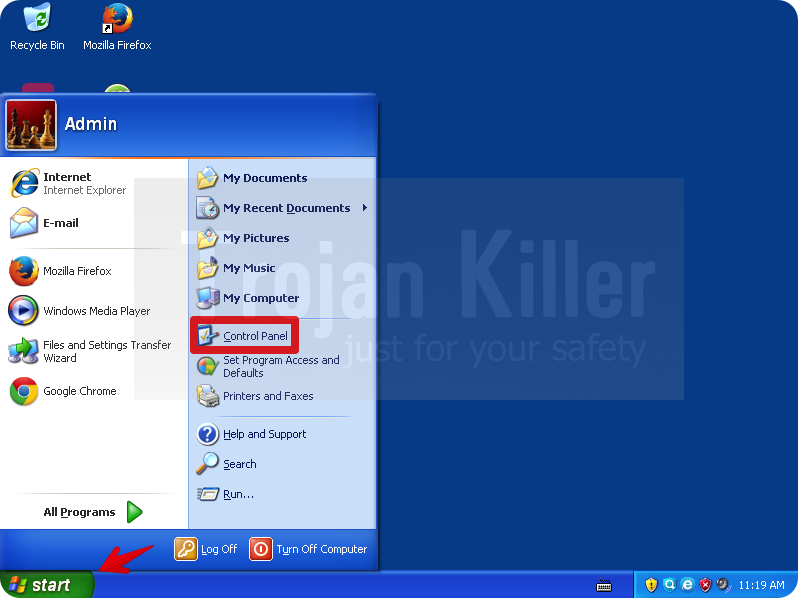
- Click on “Start” and go to the “Control Panel“:
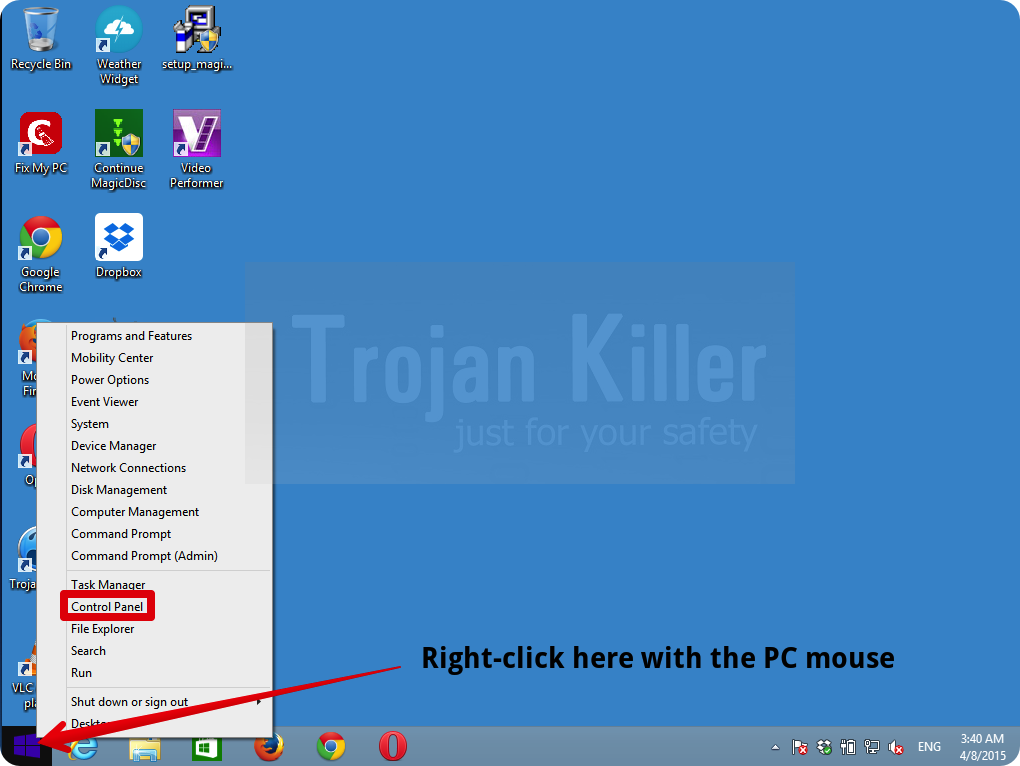
- To access the Control Panel in Windows 8 operating system move the computer mouse towards the left bottom hot corner of Windows 8 screen and right-click on it. In Windows 8.1, simply right-click on the “Start” button. Then click on “Control Panel“:
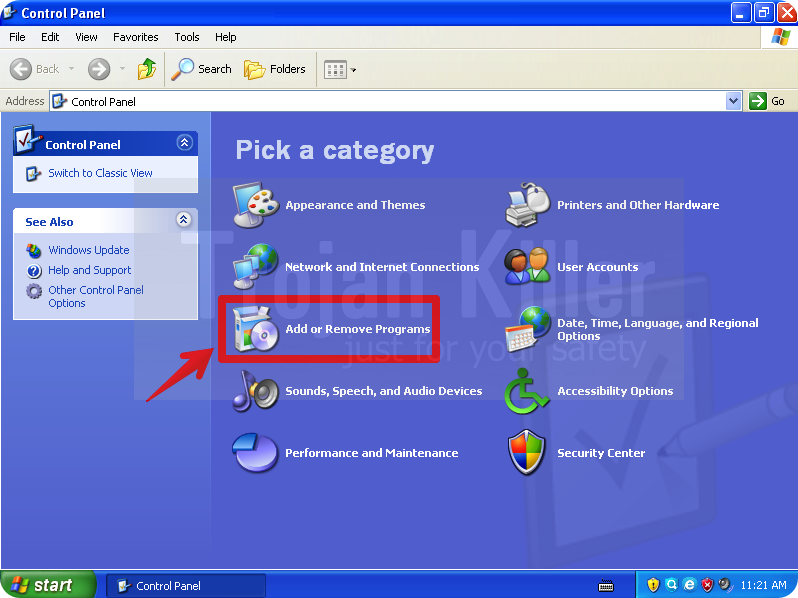
- In Windows XP click on “Add or remove programs“:
- In Windows Vista, 7, 8 and 8.1 click on “Uninstall a program“:
- Uninstall any suspicious applications which may be related to Esurf.biz. To do it, in Windows XP click “Remove” button related to such applications. In Windows Vista, 7, 8 and 8.1 right-click on certain suspicious program with the PC mouse and click on “Uninstall / Change“.
Step 2. Removing suspicious elements from the list of add-ons and extensions of your browser.
In addition to removal of suspicious programs from the Control Panel of your PC as explained above, you also need to remove suspicious items from the add-ons or extensions of your browser. Please follow this guide for managing browser add-ons and extensions for more detailed information. Remove any items related to this browser hijacker and other unwanted applications installed on your PC.
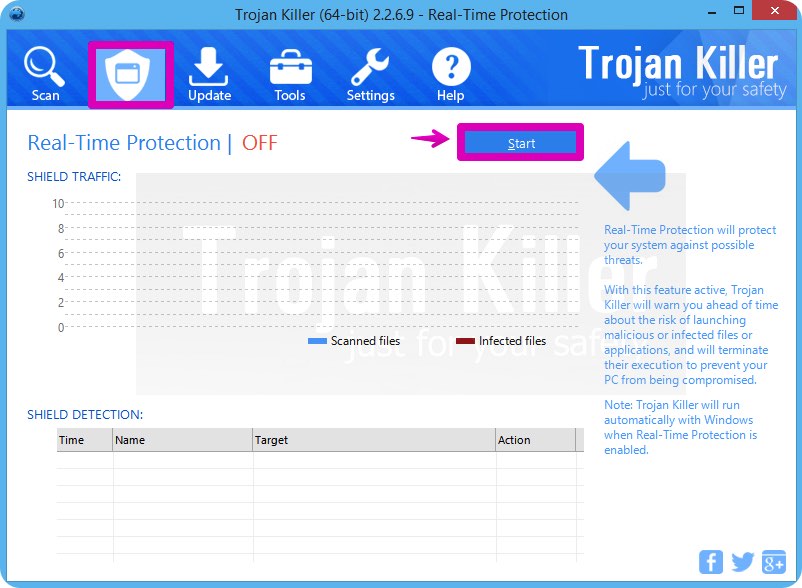
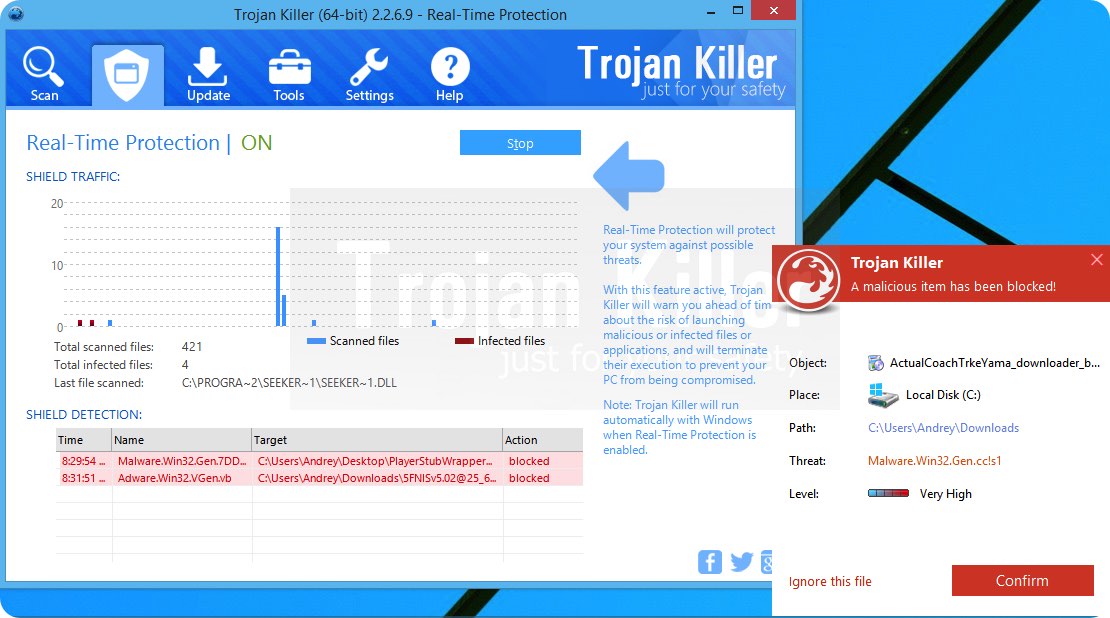
How to prevent your PC from being reinfected:
Plumbytes Anti-Malware offers a superb service to prevent malicious programs from being launched in your PC ahead of time. By default, this option is disabled once you install Anti-Malware. To enable the Real-Time Protection mode click on the “Protect” button and hit “Start” as explained below:
Once this option is enabled, your computer will be protected against all possible malware attacking your PC and attempting to execute (install) itself. You may click on the “Confirm” button to continue blocking this infected file from being executed, or you may ignore this warning and launch this file.