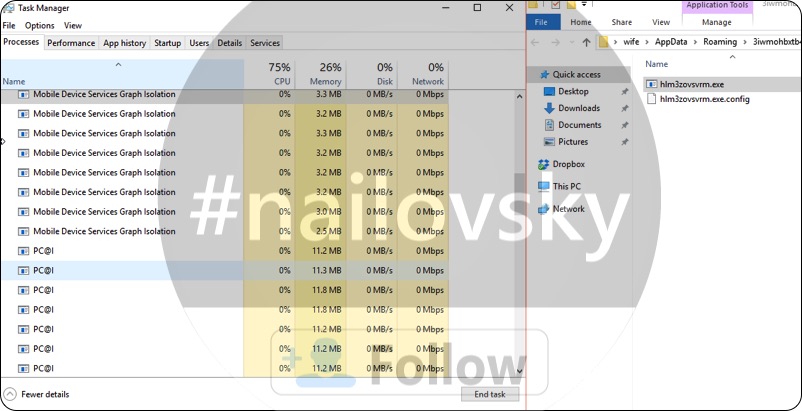
Mobile Device Services Graph Isolation is an extremely dangerous process that can be found enabled in your computer. This particular process is a part of certain nasty adware that some way or another made itself the part of your computer. You may notice that there are plenty of annoying ads and advertisement banners popping up everywhere in your screen. Furthermore, your browser gets regularly redirected to all kinds of other unsafe places in the world wide web. Your system will be functioning extremely sluggish. We strongly advise that you carefully follow this guide below to get your system properly cleaned.
Quick menu to help you navigate through Mobile Device Services Graph Isolation removal guide.
Removal guide for Mobile Device Services Graph Isolation malware.
Additional manual fixes for your browsers after malware attack.
Mobile Device Services Graph Isolation may get into your computer during installation of certain free applications which may be downloaded through various freeware resources online. The sad truth is that even some of the world’s reliable freeware download websites like CNet may offer installation of additional software that is not intended to be installed by users in the first place. This is sort of a payment that user pays for installation of that free application. In order to avoid intrusion of such potentially unwanted applications it is very important for you to carefully read the installation guidelines related to all free programs you intend to make the part of your computer. In case you read the information about some extra applications suggested for default installation, your immediate action should be to switch to the advanced (custom) installation mode where you will have a chance to uncheck this additional software from penetrating into your system. Sadly, often people fail to be careful and permit different absolutely unwanted and sometimes even dangerous utilities to be injected into the system.
Finally, another reason why Mobile Device Services Graph Isolation is now in your computer is because your security software (anti-virus program) did not perform its direct function of protecting your system from malware attacks. This most likely happened because of poorly updated database of your anti-virus, so definitely it is time for you to switch to some other program that will help you avoid the cases of your system to be infected with malware in future.
Mobile Device Services Graph Isolation will essentially slow down the performance of your computer. In fact, there could be plenty of such processes running simultaneously, which may result in absolute failure of your computer to function in a proper manner. Hence, our strong admonition for you is to perform a thorough scanning of your computer with a proven malware removal software named Trojan
Killer Portable a explained in the rest of the guide below.
Mobile Device Services Graph Isolation removal instructions.
This slider below shows how to use Trojan Killer Portable for Mobile Device Services Graph Isolation detection and removal:
Step-by-step guidelines.
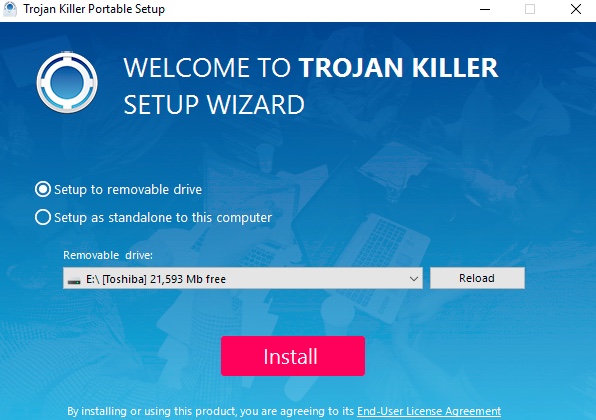
- Step 1. Download Trojan Killer Portable via the download button below:
- Step 2. Click on “Install” button and proceed with its installation process.
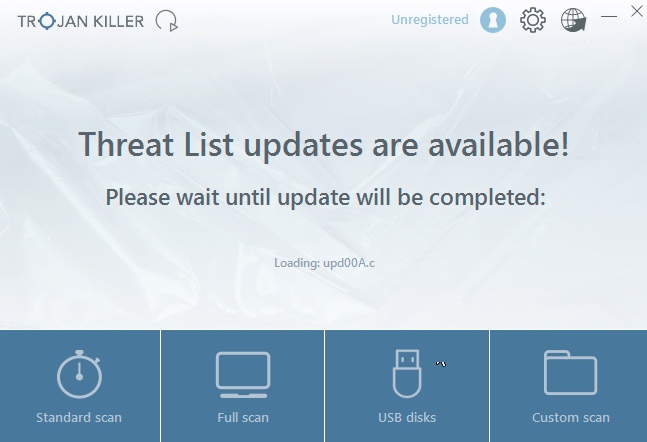
- Step 3. Select scan type.
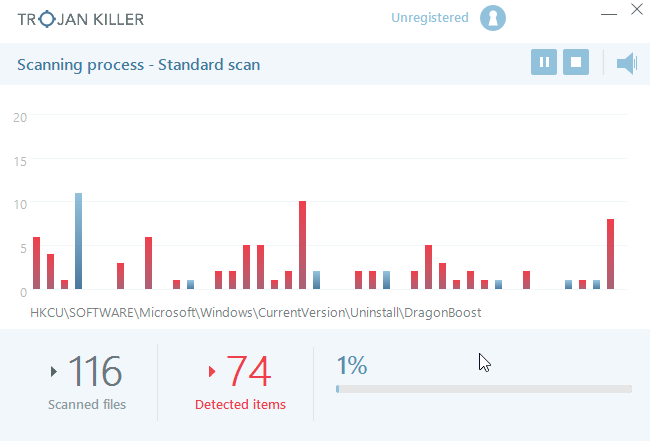
- Step 4. Software will begin scanning your system.
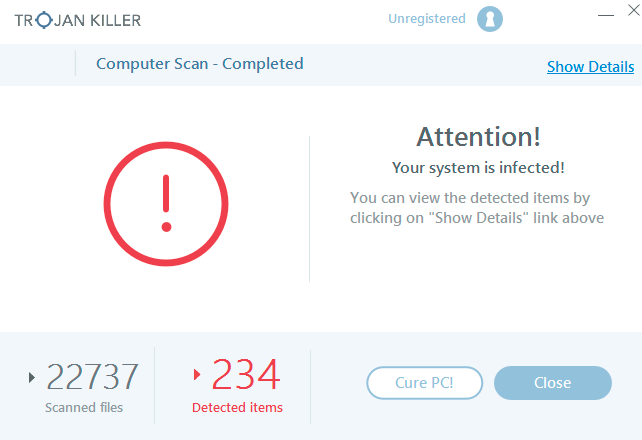
- Step 5. Click on “Cure PC“.
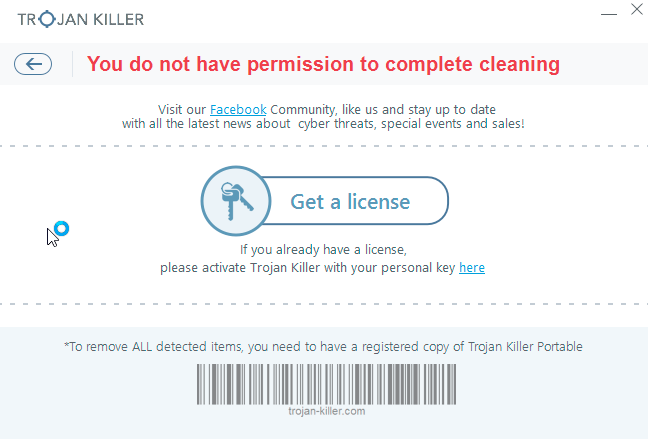
- Step 6. Click on “Get a license“.
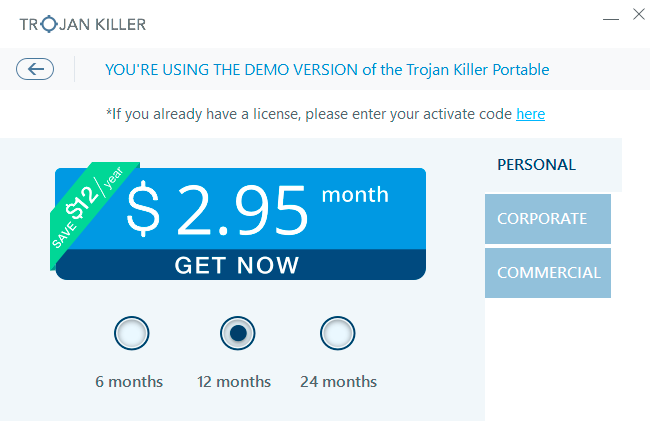
- Step 7. Select license term and purchase the program to remove malware.
Solution to protect your computer from getting contaminated with Mobile Device Services Graph Isolation and similar threats in the future:
With millions of malicious applications currently in the web people definitely need powerful security solutions for their PCs. You could have avoided all negative side effects related to unwanted intrusion of adware with the help of Trojan Killer Portable, so we strongly advise that you buy Trojan Killer Portable now!
After you eliminate Mobile Device Services Graph Isolation malware it is mandatory to apply additional manual fixes to clean your browsers from malware traces.
[TABS_R id=7864]