Windows AntiBreach Patrol is one more virus program that causes a lot of troubles for people who have it on their PCs. It tends to attack computers worldwide and steal money from the gullible Internet users. It invisibly infiltrates into the vulnerable system, arranges fake system checkup, and scares the potential victims with invented scan reports. It tries to trick the payment out in such way. Go on reading to know more about this malware.
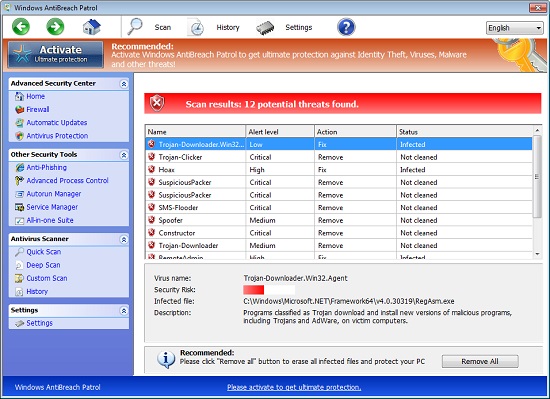
After successful installation it initiates fake system scan of your PC and displays falsified scan reports. Plenty of viruses inside of your computer are detected during these pseudo system checkups. Keep in mind the fact that Windows Anti Breach Patrol is trying to mislead you. This is why its reports are invented and problems it finds do not exist in reality. So, do not panic, because panic is the best thing you can ever do for cyber crooks. At the moment when you are in desperation Windows AntiBreach Patrol offer to buy the registered version is allegedly able to kill all declared viruses. Do not trust all such fictitious promises made by Windows AntiBreach Patrol malware. Neither full version nor trial one is capable for anything good because it is the scam.
Do not believe even a word said by this parasite. It cannot eliminate any problems; it is quite good at causing them. Be advised enough not to be tricked in such way and not to waste money for such scam. You should neutralize this pest at once. The instructions on how to remove Windows AntiBreach Patrol are stipulated below. Here you will find its automatic removal tutorial. If you have any problems trying to get rid of it, please let us know.
Software necessary for Windows AntiBreach Patrol virus removal:
Windows AntiBreach Patrol removal steps:
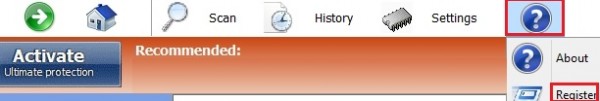
- In Windows AntiBreach Patrol click “?” Menu button anc click “Register”:
- Paste this product key – 0W000-000B0-00T00-E0022 exactly as shown at the image below, then click “Register“:
- 0W000-000B0-00T00-E0001
- 0W000-000B0-00T00-E0002
- 0W000-000B0-00T00-E0003
- 0W000-000B0-00T00-E0021
- Afer registration download Plumbytes Anti-Malware without any restrictions on the part of the rogue, scan your PC with Plumbytes Anti-Malware and remove all infections detected by clicking “Apply” button at the end of scan.
- Restart your computer and repeat scan.

Note! If this product key has been found to be invalid, try one of these keys as well:
Windows AntiBreach Patrol similar removal video at YouTube:
Beware of ways how Windows AntiBreach Patrol is spread today:
Windows AntiBreach Patrol uses various vulnerabilities of browsers like Internet Explorer, Google Chrome, Mozilla Firefox, Opera and many others for the interference into your computer. For example, you might get the following scary alert, supposedly coming from Microsoft Antivirus:
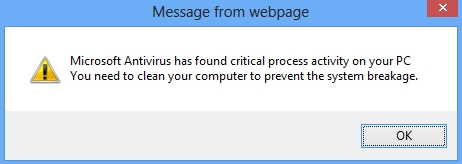
Microsoft Antivirus has found critical process activity on your PC. You will need to clean your computer to prevent the system breakage.
If you actually click the “OK” button as shown at the image you will have another fake alert, not associated at all to Microsoft Security Essential Alert, but yet claiming to be such:
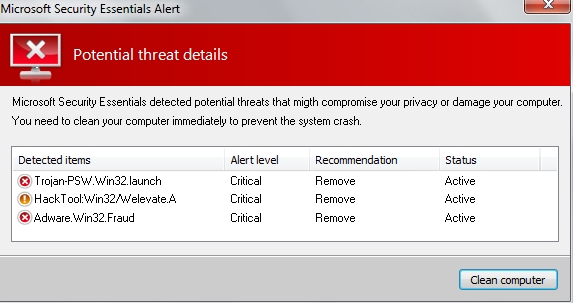
Microsoft Security Essentials Alert
Potential threat details
Microsoft Security Essentials detected potential threats that might compromise your privacy or damage your computer. You need to clean your computer immediately to prevent the system crash.
Detected items:
– Trojan-PSW.Win32.launch
– HackTool:Win32/Welevate.A
– Adware.Win32.Fraud
Associated files and registry entries:
Related files:
%AppData%\svc-[rnd].exe
%CommonAppData%\connector.swf
%Programs%\Windows AntiBreach Patrol.lnk
%Desktop%\Windows AntiBreach Patrol.lnk
Related registry entries:
HKCU\Software\Microsoft\Windows\CurrentVersion\Run\PrSft %AppData%\svc-[rnd].exe
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\MSASCui.exe
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\MSASCui.exe\Debugger svchost.exe
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\MpCmdRun.exe
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\MpCmdRun.exe\Debugger svchost.exe
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\MpUXSrv.exe
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\MpUXSrv.exe\Debugger svchost.exe
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\k9filter.exe
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\k9filter.exe\Debugger svchost.exe
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\msconfig.exe
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\msconfig.exe\Debugger svchost.exe
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\msmpeng.exe
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\msmpeng.exe\Debugger svchost.exe
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\msseces.exe
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\msseces.exe\Debugger svchost.exe
Fake security alerts, notifications and warnings of Windows AntiBreach Patrol scam:
Firewall has blocked a program from accessing the Internet
C:\Program Files\Internet Explorer\iexplore.exe
is suspected to have infected your PC.
This type of virus intercepts entered data and transmits them
to a remote server.
Error
Trojan activity detected. System integrity at risk.
Full system scan is highly recommended.
Error
System data security is at risk!
To prevent potential PC errors, run a full system scan.