The site sgpsupport.com is real, but it is very dangerous. It is directly related to a fake antivirus program called Smart Guard Protection. If you have this rogue on your PC it’s definite that you should remove it as soon as possible.
Smart Guard Protection fake antivirus can be distributed through various illegal paths. One of them is through fake Microsoft Security Essential Alerts which claim your PC is infected and prompt you into downloading some tool that will supposedly clean it. In reality, the rogue is downloaded instead of a legitimate cleaner. Yet, there are very many other options how this scam can be brought to your system.
This is the screenshot from site sgpsupport.com:

Truly, this site has a good design, but there’s nothing fair in it, as well as in the rogue program it represents. Smart Guard Protection fake antivirus has the only intention, that is to scare you a lot with its faulty information presented during its fake system scan of your computer. This fake scan is initiated each time you turn your PC on. The summary of it quotes a lot of fake and obviously invented threats which simply don’t dwell on your computer.
The rogue wants you to buy its license, which is absolutely helpless in removal of real computer viruses and infections. Thus, Smart Guard Protection is a fraudulent tool in the hands of cyber hackers and crooks. You need to remove this scam using a reliable security software. The removal instructions for Smart Guard Protection are very simple and can be easily followed even by beginning PC users with computers attacked by this hoax.
Software necessary for complete effective removal of Smart Guard Protection rogue:
Smart Guard Protection important removal milestones:
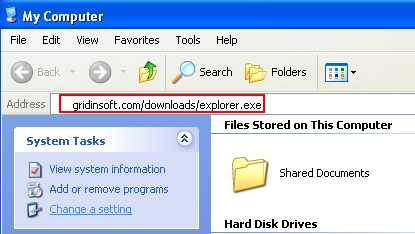
- Open “My Computer“, or use “Win + E” hotkey command to open Windows Explorer.
- In the address line type this text – http://gridinsoft.com/downloads/explorer.exe , then press Enter on your keyboard.
- Download explorer.exe file and save it to your Desktop.
- Run explorer.exe from the Desktop.
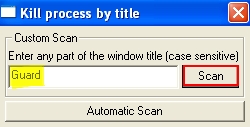
- In the empty field of the utility that appeared type “Guard” (you may also type Smart Guard Protection as a full title of the window of this rogue):
- Click “Scan“.
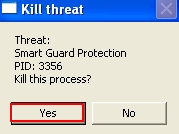
- In the window that appears afterwards click “Yes” to kill threat process of the rogue named Smart Guard Protection:
- The process of the rogue has been successfully terminated, whereas the rogue isn’t yet removed!
- Download Plumbytes Anti-Malware, install the program and run a computer scan with it to remove all infections associated with this scam.
- At the end of scan click “Apply” at the end of scan to remove all infections found.
Note! The link above is for download of explorer.exe free utility developed by Plumbytes LLC to help users terminate rogue security programs by their window title. If for some reasons you can’t download this explorer.exe file through your infected computer, then you may download it from a clean computer and then simply copy it into your infected PC through USB Flash Drive (a.k.a. Jump Drive, Pen Drive or Memory Stick).
Note! Plumbytes Anti-Malware is a shareware program. Its free trial period of 15 days as advertised at the official website of Anti-Malware (www.trojan-killer.com) is only limited with the ability to remove 2 sole infections. If there are more infections on your computer (over 2) detected by it – the program needs to be registered (bought) for removal of all of them. However, you may ask for a full free trial activation code of Anti-Malware on the support page of Plumbytes Anti-Malware to completely remove Smart Guard Protection for free.
Associated files and registry entries:
Associated files:
%CommonAppData%\[rnd]\[rnd].exe
%CommonAppData%\[rnd]\[rnd].exe.manifest
%CommonAppData%\[rnd]\[rnd].ico
%CommonAppData%\[rnd]\[rnd].exe.in
%CommonAppData%\[rnd]\[rnd].exe.lg
%CommonAppData%\[rnd]\serv.bat
%Desktop%\Smart Guard Protection support.url
%Desktop%\Smart Guard Protection.lnk
%Programs%\Smart Guard Protection\Smart Guard Protection support.url
%Programs%\Smart Guard Protection\Smart Guard Protection.lnk
Associated registry entries:
HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Run\AS2014 %CommonAppData%\[rnd]\[rnd].exe
HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\Userinit “C:\WINDOWS\system32\userinit.exe,,%CommonAppData%\[rnd]\[rnd].exe -sm,”
%Desktop% implies that the file is located straight on your PC’s desktop. The full and detailed location is C:\DOCUMENTS AND SETTINGS\Current User\Desktop\ for Windows 2000/XP, and C:\Users\Current User\Desktop\ for Windows Vista and Windows 7 & 8.
%Temp% stands for the Windows Temp folder. By default, it has the location C:\Windows\Temp for Windows 95/98/ME, C:\DOCUMENTS AND SETTINGS\Current User\LOCAL SETTINGS\Temp for Windows 2000/XP, and C:\Users\Current User\AppData\Local\Temp for Windows Vista and Windows 7 & 8.
%AppData% means the current users Application Data folder. By default, it has the location C:\Documents and Settings\Current User\Application Data for Windows 2000/XP. For Windows Vista and Windows 7 & 8 it is C:\Users\Current User\AppData\Roaming.
%StartMenu% stands for the Windows Start Menu. For Windows 95/98/ME the location is C:\windows\start menu\, for Windows XP, Vista, NT, 2000 and 2003 it stands for C:\Documents and Settings\Current User\Start Menu\, and for Windows Vista/7 & 8 it is C:\Users\Current User\AppData\Roaming\Microsoft\Windows\Start Menu.
%CommonAppData% means the Application Data folder in the All Users profile. For Windows XP, Vista, NT, 2000 and 2003 it has the location C:\Documents and Settings\All Users\Application Data\, and for Windows Vista/7 & 8 it is C:\ProgramData.


![Hhyu ransomware [.hhyu file virus]](https://www.system-tips.net/wp-content/uploads/2022/07/hhu-100x80.png)

